- Table View
- List View
The Book Bible: How to Sell Your Manuscript—No Matter What Genre—Without Going Broke or Insane
by Susan ShapiroA Brilliant, Buoyant Guide to Publishing Your Book Hundreds of thousands of books come out every year worldwide. So why not yours? In The Book Bible, New York Times bestseller and wildly popular Manhattan writing professor Susan Shapiro reveals the best and fastest ways to break into a mainstream publishing house. Unlike most writing manuals that stick to only one genre, Shapiro maps out the rules of all the sought-after, sellable categories: novels, memoirs, biography, how-to, essay collections, anthologies, humor, mystery, crime, poetry, picture books, young adult and middle grade, fiction and nonfiction. Shapiro once worried that selling 16 books in varied sub-sections made her a literary dabbler. Yet after helping her students publish many award-winning bestsellers on all shelves of the bookstore, she realized that her versatility had a huge upside. She could explain, from personal experience, the differences in making each kind of book, as well as ways to find the right genre for every project and how to craft a winning proposal or great cover letter to get a top agent and book editor to say yes. This valuable guide will teach both new and experienced scribes how to attain their dream of becoming a successful author.
The Book Of Myself: A Do-It Yourself Autobiography in 201 Questions
by David Marshall Carl MarshallHave you ever wanted to create your own autobiography or wished you had the life stories of a relative or friend? Now beautifully revised and updated, The Book of Myself is a do-it-yourself memoir that helps you record and preserve the experiences and knowledge of a lifetime for years to come. Divided into Early, Middle, and Later Years, this keepsake volume contains 201 questions that guide you through the process of keeping memories on subjects such as family and friends, learning and education, work and responsibilities, and the world around you. Created by a grandson and grandfather, The Book of Myself is the perfect way for you, or someone close to you, to remember the turning points and everyday recollections of a lifetime and share them with future generations.
The Book Proposal Book: A Guide for Scholarly Authors (Skills for Scholars)
by Laura Portwood-StacerA step-by-step guide to crafting a compelling scholarly book proposal—and seeing your book through to successful publicationThe scholarly book proposal may be academia’s most mysterious genre. You have to write one to get published, but most scholars receive no training on how to do so—and you may have never even seen a proposal before you’re expected to produce your own. The Book Proposal Book cuts through the mystery and guides prospective authors step by step through the process of crafting a compelling proposal and pitching it to university presses and other academic publishers.Laura Portwood-Stacer, an experienced developmental editor and publishing consultant for academic authors, shows how to select the right presses to target, identify audiences and competing titles, and write a project description that will grab the attention of editors—breaking the entire process into discrete, manageable tasks. The book features over fifty time-tested tips to make your proposal stand out; sample prospectuses, a letter of inquiry, and a response to reader reports from real authors; optional worksheets and checklists; answers to dozens of the most common questions about the scholarly publishing process; and much, much more.Whether you’re hoping to publish your first book or you’re a seasoned author with an unfinished proposal languishing on your hard drive, The Book Proposal Book provides honest, empathetic, and invaluable advice on how to overcome common sticking points and get your book published. It also shows why, far from being merely a hurdle to clear, a well-conceived proposal can help lead to an outstanding book.
The Book Publishing Industry (Mass Communications Book Ser.)
by Albert N. GrecoThe Book Publishing Industry focuses on consumer books (adult, juvenile, and mass market paperbacks) and reviews all major book categories to present a comprehensive overview of this diverse business. In addition to the insights and portrayals of the U.S. publishing industry, this book includes an appendix containing historical data on the industry from 1946 to the end of the twentieth century. The selective bibliography includes the latest literature, including works in marketing and economics that has a direct relationship with this dynamic industry. This third edition features a chapter on e-books and provides an overview of the current shift toward digital media in the US book publishing industry.
The Book in Africa
by David Johnson Caroline DavisThis volume presents new research and critical debates in African book history, and brings together a range of disciplinary perspectives by leading scholars in the subject. It includes case studies from across Africa, ranging from third-century manuscript traditions to twenty-first century internet communications.
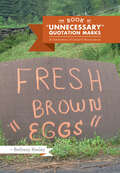
The Book of "Unnecessary" Quotation Marks: A Celebration of Creative Punctuation
by Bethany KeeleyFrom the popular blog, a hilarious and horrifying survey of quotation mark abuse in all its forms.From the sarcastic to the suggestive, here are quotation marks as we love them best, doing horrible damage to the English language. Who wouldn’t have second thoughts about ordering the “hamburger” on the diner’s menu? Would it be best to skip the “blowout” sale at the department store? What hidden price must be paid for something marked “free”? Assembled by the creator of the wildly popular “Blog” of “Unnecessary” Quotation Marks, this book surveys the havoc wreaked by quotation marks on signs, menus, placards, and posters that leave reality upended by supposed “facts.” This smarty-pants guide is “perfect” for desperate grammarians, habitual air quoters, and anyone who appreciates a good laugh.
The Book of Agreement: 10 Essential Elements for Getting the Results You Want
by Stewart LevineCrafting agreements with others is a fundamental life skill. Unfortunately, we were never taught how to do it. The agreements most people make are incomplete and ineffective-they usually focus on protecting against what might go wrong instead of figuring out how to make things go right. The Book of Agreement offers a new approach. Stewart Levine demonstrates the superiority of "agreements for results" versus "agreements for protection" and outlines ten principles for creating agreements that explicitly articulate desired outcomes and provide a roadmap to achieving them. He includes over thirty specific templates that can be used to create this new type of agreement for results in a variety of organizational and personal contexts.
The Book of Boundaries: Set the Limits That Will Set You Free
by Melissa UrbanEnd resentment, burnout, and anxiety—and reclaim your time, energy, health, and relationships. As the co-founder of the Whole30, Melissa Urban helped millions of people transform their relationship with food. Now, in this powerful and practical guide to setting boundaries, she shows you how to prioritize your needs and revolutionize your relationships.&“Melissa Urban shows the way forward with clarity, vulnerability, and humor.&” —Gretchen Rubin, New York Times bestselling author of The Happiness Project and The Four TendenciesDo your relationships often feel one-sided or unbalanced? Are you always giving in just so things will go smoothly? Do you wish you could learn to say no—but, like, nicely? Are you depleted, overwhelmed, and tired of putting everyone else&’s needs ahead of your own? If you answered yes to any of these questions, you need to establish some boundaries.Since launching the mega-bestselling wellness program the Whole30, Melissa Urban has taught millions of people how to establish healthy habits and successfully navigate pushback and peer pressure. She knows firsthand that boundaries—clear limits you set to protect your energy, time, and health—are the key to feelings of security, confidence, and freedom in every area of your life.Now, in The Book of Boundaries, she shows you how boundaries are the key to better mental health, increased energy, improved productivity, and more fulfilling relationships.In her famously direct and compassionate style, Urban offers:• 130+ scripts with language you can use to instantly establish boundaries with bosses and co-workers, romantic partners, parents and in-laws, co-parents, friends, family, neighbors, strangers—and yourself• actionable advice to help you communicate your needs with clarity and compassion• tips for successfully navigating boundary guilt, pushback, pressure, and oversteps• techniques to create healthy habits around food, drink, technology, and moreUser-friendly and approachable, The Book of Boundaries will give you the tools you need to stop justifying, minimizing, and apologizing, leading you to more rewarding relationships and a life that feels bigger, healthier, and freer.
The Book of Boundaries: Set the Limits That Will Set You Free
by Melissa UrbanNEW YORK TIMES BESTSELLER FROM THE CO-FOUNDER OF THE WHOLE30 • End resentment, burnout, and anxiety—and reclaim your time, energy, health, and relationships. &“Melissa Urban shows the way forward with clarity, vulnerability, and humor.&”—Gretchen Rubin, author of Life in Five Senses Melissa Urban has helped millions of people transform their relationship with food. Now, in this powerful and practical guide, she shows how boundaries—clear limits you set to protect your energy, time, and health—are the key to feelings of security, confidence, and freedom in every area of your life. In her famously direct and compassionate style, Urban offers: • 130+ scripts with language you can use to set boundaries with bosses and co-workers, romantic partners, parents and in-laws, co-parents, friends, family, neighbors, strangers—and yourself • Actionable advice to help you communicate your needs with clarity and compassion • Tips for successfully navigating boundary guilt, pushback, pressure, and oversteps • Techniques to create healthy habits around food, drink, technology, and moreUser-friendly and approachable, The Book of Boundaries will give you the tools you need to stop justifying, minimizing, and apologizing, leading you to more rewarding relationships and a life that feels bigger, healthier, and freer. ONE OF THE BEST BOOKS OF THE YEAR: Mindful
The Book of Business Awesome / The Book of Business UnAwesome
by Scott Stratten Alison KramerUnAwesome is UnAcceptable. The Book of Business Awesome is designed as two short books put together—one read from the front and the other read from the back when flipped over. Covering key business concepts related to marketing, branding, human resources, public relations, social media, and customer service, The Book of Business Awesome includes case studies of successful businesses that gained exposure through being awesome and effective. This book provides actionable tools enabling readers to apply the concepts immediately to their own businesses. The flip side of the book, The Book of Business UnAwesome, shares the train-wreck stories of unsuccessful businesses and showcases what not to do. Key concepts include the power of peripheral referrals and how to create content for your "third circle" Explains how to re-recruiting your employees and re-court your customers Ensure that your business remains awesome, instead of unawesome, and apply these awesomely effective strategies to your business today.
The Book of Lost Books: An Incomplete History of All the Great Books You'll Never Read
by Stuart KellyA &“clever and highly entertaining&” look at books through history that were stolen, went missing, or just never got written (The New York Times). In an age when deleted scenes from Adam Sandler movies are saved, it&’s sobering to realize that some of the world&’s great prose and poetry has gone missing. This witty and unique new book rectifies that wrong. Part detective story, part history, part exposé, The Book of Lost Books is the first guide to literature&’s what-ifs and never-weres. In compulsively readable fashion, this book reveals details about tantalizing vanished works by the famous, acclaimed, and influential, from the time of cave drawings to the late twentieth century. Here are true stories behind stories, poems, and plays that now exist only in imagination: ·Aristophanes&’ Heracles, the Stage Manager was one of the playwright&’s several spoofs that disappeared. ·Love&’s Labours Won may have been a sequel to Shakespeare&’s Love&’s Labours Lost—or was it just an alternative title for The Taming of the Shrew? ·Jane Austen&’s incomplete novel Sanditon was a critique of hypochondriacs and cures started when the author was fatally ill. ·Nikolai Gogol burned the second half of Dead Souls after a religious conversion convinced him that literature was paganism. ·Some of the thousand pages of William Burroughs&’s original Naked Lunch were stolen and sold on the street by Algerian street boys. ·Sylvia Plath&’s widower, Ted Hughes, claimed that the 130 pages of her second novel, perhaps based on their marriage, were lost after her death. Whether destroyed (Socrates&’ versions of Aesop&’s Fables), misplaced (Malcolm Lowry&’s Ultramarine, pinched from his publisher&’s car), interrupted by the author&’s death (Robert Louis Stevenson&’s Weir of Hermiston), or simply never begun (Vladimir Nabokov&’s Speak, America, a second volume of his memoirs), these missing links create a history of literature for a parallel world. Civilized, satirical, erudite yet accessible, The Book of Lost Books is a real find.
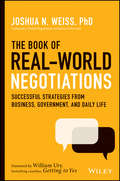
The Book of Real-World Negotiations: Successful Strategies From Business, Government, and Daily Life
by Joshua N. WeissReal world negotiation examples and strategies from one of the most highly respected authorities in the field This unique book can help you change your approach to negotiation by learning key strategies and techniques from actual cases. Through hard to find real world examples you will learn exactly how to effectively and productively negotiate. The Book of Real World Negotiations: Successful Strategies from Business, Government and Daily Life shines a light on real world negotiation examples and cases, rather than discussing hypothetical scenarios. It reveals what is possible through preparation, persistence, creativity, and taking a strategic approach to your negotiations. Many of us enter negotiations with skepticism and without understanding how to truly negotiate well. Because we lack knowledge and confidence, we may abandon the negotiating process prematurely or agree to deals that leave value on the table. The Book of Real World Negotiations will change that once and for all by immersing you in these real world scenarios. As a result, you&’ll be better able to grasp the true power of negotiation to deal with some of the most difficult problems you face or to put together the best deals possible. This book also shares critical insights and lessons for instructors and students of negotiation, especially since negotiation is now being taught in virtually all law schools, many business schools, and in the field of conflict resolution. Whether you&’re a student, instructor, or anyone who wants to negotiate successfully, you&’ll be able to carefully examine real world negotiation situations that will show you how to achieve your objectives in the most challenging of circumstances. The cases are organized by realms—domestic business cases, international business cases, governmental cases and cases that occur in daily life. From these cases you will learn more about: Exactly how to achieve Win-Win outcomes The critical role of underlying interests The kind of thinking that goes into generating creative options How to consider your and the other negotiator&’s Best Alternative to a Negotiated Agreement (BATNA) Negotiating successfully in the face of power Achieving success when negotiating cross-culturally Once you come to understand through these cases that negotiation is the art of the possible, you&’ll stop saying "a solution is impossible." With the knowledge and self-assurance you gain from this book, you&’ll roll up your sleeves and keep negotiating until you reach a mutually satisfactory outcome!
The Book of Things
by Brian Henry Ales StegerFrom his first book of poems, Chessboards of Hours (1995), Aleš Šteger has been one of Slovenia's most promising poets. The philosophical and lyrical sophistication of his poems, along with his work as a leading book editor and festival organizer, quickly spread Šteger's reputation beyond the borders of Slovenia. The Book of Things is Šteger's most widely praised book of poetry and his first American collection. The book consists of fifty poems that look at "things" (i.e. aspirin, chair, cork) which are transformed by Šteger's unique poetic alchemy.Translator Brian Henry is a distinguished poet, translator, editor, and critic.From Publisher's Weekly:Steger's efforts sometimes bring to mind such Western European figures as Francis Ponge and Craig Raine, who also sought to make household things look new and strange. Yet Steger brings a melancholy Central European sense of history- his objects tend to remember, or cause, great pain: "It pours, this poisonous, sweet force," Steger writes of "Saliva," "Between teeth, when you spit your own little genocide." (Nov.)From Guernica, a Magazine of Art and Politics:It is a rare treat to have an English translation before the ink has dried on the original. By which I mean, a mere five years after the book's Slovenian publication, Brian Henry has brought these poems to life for those of us not lucky enough to read Slovenian. Henry's translations are impressive for sheer acrobatics.
The Book of Things (Lannan Translations Selection Series #18)
by Ales StegerFrom his first book of poems, Chessboards of Hours (1995), Aleš Šteger has been one of Slovenia's most promising poets. The philosophical and lyrical sophistication of his poems, along with his work as a leading book editor and festival organizer, quickly spread Šteger's reputation beyond the borders of Slovenia. The Book of Things is Šteger's most widely praised book of poetry and his first American collection. The book consists of fifty poems that look at "things" (i.e. aspirin, chair, cork) which are transformed by Šteger's unique poetic alchemy.Translator Brian Henry is a distinguished poet, translator, editor, and critic.From Publisher’s Weekly:Steger’s efforts sometimes bring to mind such Western European figures as Francis Ponge and Craig Raine, who also sought to make household things look new and strange. Yet Steger brings a melancholy Central European sense of history- his objects tend to remember, or cause, great pain: "It pours, this poisonous, sweet force,” Steger writes of "Saliva,” "Between teeth, when you spit your own little genocide.” (Nov.)From Guernica, a Magazine of Art and Politics:It is a rare treat to have an English translation before the ink has dried on the original. By which I mean, a mere five years after the book’s Slovenian publication, Brian Henry has brought these poems to life for those of us not lucky enough to read Slovenian. Henry’s translations are impressive for sheer acrobatics.
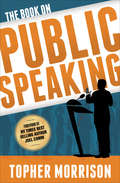
The Book on Public Speaking
by Topher Morrison&“One of the most powerful professional speakers in America . . . reveals how he&’s earned millions onstage, on camera and in business&” (Steve Siebold, CSP, past chairman of The National Speakers Association&’s Million Dollar Speakers Group). If you look at the trends of over thirty years ago in fashion, technology, architecture, and any other industry, what was cutting edge back then has become cliché and grossly out of date now. But in the speaking industry, most people get up and still walk, talk, and sound like the 1980s motivational speakers of yesteryear. The Book on Public Speaking takes a head-on approach and challenges the status quo for business leaders that speak in front of their staff, board of directors, and the public. After reading this book you will be privy to the most current methods for speaking to an audience for maximum impact in today&’s more sophisticated and skeptical culture. If you are the type of business leader who has achieved a level of success in life and feel compelled to share your story with the world, don&’t lessen that impact by imitating outdated speaking techniques. Instead, break the mold of the speaker cliché and tap into a speaking style that is authentic, packs a punch, and leaves the audience wanting more. &“I learned some amazing presentation techniques from Topher. I&’m using them right now. They&’re awesome. You can&’t tell because you&’re reading this.&” —John Heffron, winner of The Last Comic Standing &“Morrison is crazy good at training you how to communicate on-camera so that your business gets more attention.&” —James Lavers, professional speaker, founder, &“Selling from the Screen&”
The Bookseller of Kabul
by Asne Seierstad Ingrid ChristophersenAn unusually intimate glimpse of a typical Afghan family, gleaned from the author's 3-month stay with the bookseller's family. With a list of questions for reading groups.
The Bookseller's Tale
by Martin LathamA SPECTATOR AND EVENING STANDARD BOOK OF THE YEAR 2020'A joy. Each chapter instantly became my favourite' David Mitchell, author of Cloud Atlas'Wonderful' Lucy Mangan'The right book has a neverendingness, and so does the right bookshop.'This is the story of our love affair with books, whether we arrange them on our shelves, inhale their smell, scrawl in their margins or just curl up with them in bed. Taking us on a journey through comfort reads, street book stalls, mythical libraries, itinerant pedlars, radical pamphleteers, extraordinary bookshop customers and fanatical collectors, Canterbury bookseller Martin Latham uncovers the curious history of our book obsession - and his own. Part cultural history, part literary love letter and part reluctant memoir, this is the tale of one bookseller and many, many books.'If ferreting through bookshops is your idea of heaven, you'll get the same pleasure from this treasure trove of a book' Jake Kerridge, Sunday Express
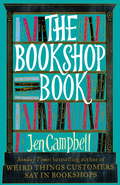
The Bookshop Book
by Jen CampbellWe're not talking about rooms that are just full of books. We're talking about bookshops in barns, disused factories, converted churches and underground car parks. Bookshops on boats, on buses, and in old run-down train stations. Fold-out bookshops, undercover bookshops, this-is-the-best-place-I've-ever-been-to-bookshops. Meet Sarah and her Book Barge sailing across the sea to France; meet Sebastien, in Mongolia, who sells books to herders of the Altai mountains; meet the bookshop in Canada that's invented the world's first antiquarian book vending machine. And that's just the beginning. From the oldest bookshop in the world, to the smallest you could imagine, The Bookshop Book examines the history of books, talks to authors about their favourite places, and looks at over three hundred weirdly wonderful bookshops across six continents (sadly, we've yet to build a bookshop down in the South Pole). The Bookshop Book is a love letter to bookshops all around the world. --"A good bookshop is not just about selling books from shelves, but reaching out into the world and making a difference." David Almond (The Bookshop Book includes interviews and quotes from David Almond, Ian Rankin, Tracy Chevalier, Audrey Niffenegger, Jacqueline Wilson, Jeanette Winterson and many, many others.)
The Bookshop Woman
by Nanako HanadaTHE BOOKSHOP WOMAN IS A LOVE STORY, A LOVE STORY ABOUT BOOKSNanako Hanada's life has not just flatlined, it's hit rock bottom... Recently separated from her husband, she is living between 4-hour capsule hostels, pokey internet cafes and bookshop floors. Her work is going no better - sales at the eccentric Village Vanguard bookstore in Tokyo, which Nanako manages, are dwindling. As Nanako's life falls apart, reading books is the only thing keeping her alive.That's until Nanako joins an online meet-up site which offers 30 minutes with someone you'll never see again. Describing herself as a sexy bookseller she offers strangers 'the book that will change their life' in exchange for a meeting. In the year that follows, Nanako meets hundreds of people, some of whom want more than just a book...Acerbic and self-knowing, The Bookshop Woman is a soul-soothing story of a bookseller's self-discovery and an ode to the joy of reading. Offering a glimpse into bookselling in Japan and the quirky side of Tokyo and its people, this is a story of how books can help us forge connection with others and lead us to ourselves.This is a story about the beauty of climbing into a book, free diving into its pages, and then resurfacing on the last page, ready to breathe a different kind of air...
The Bookshop Woman
by Nanako HanadaTHE BOOKSHOP WOMAN IS A LOVE STORY, A LOVE STORY ABOUT BOOKSNanako Hanada's life has not just flatlined, it's hit rock bottom... Recently separated from her husband, she is living between 4-hour capsule hostels, pokey internet cafes and bookshop floors. Her work is going no better - sales at the eccentric Village Vanguard bookstore in Tokyo, which Nanako manages, are dwindling. As Nanako's life falls apart, reading books is the only thing keeping her alive.That's until Nanako joins an online meet-up site which offers 30 minutes with someone you'll never see again. Describing herself as a sexy bookseller she offers strangers 'the book that will change their life' in exchange for a meeting. In the year that follows, Nanako meets hundreds of people, some of whom want more than just a book...Acerbic and self-knowing, The Bookshop Woman is a soul-soothing story of a bookseller's self-discovery and an ode to the joy of reading. Offering a glimpse into bookselling in Japan and the quirky side of Tokyo and its people, this is a story of how books can help us forge connection with others and lead us to ourselves.This is a story about the beauty of climbing into a book, free diving into its pages, and then resurfacing on the last page, ready to breathe a different kind of air...
The Bookshop of the World: Making and Trading Books in the Dutch Golden Age
by Andrew Pettegree Arthur der WeduwenThe untold story of how the Dutch conquered the European book market and became the world’s greatest bibliophiles.The Dutch Golden Age has long been seen as the age of Rembrandt and Vermeer, whose paintings captured the public imagination and came to represent the marvel that was the Dutch Republic. Yet there is another, largely overlooked marvel in the Dutch world of the seventeenth century: books.In this fascinating account, Andrew Pettegree and Arthur der Weduwen show how the Dutch produced many more books than pictures and bought and owned more books per capita than any other part of Europe. Key innovations in marketing, book auctions, and newspaper advertising brought stability to a market where elsewhere publishers faced bankruptcy, and created a population uniquely well-informed and politically engaged. This book tells for the first time the remarkable story of the Dutch conquest of the European book world and shows the true extent to which these pious, prosperous, quarrelsome, and generous people were shaped by what they read.“Book history at its best.” —Robert Darnton, New York Review of Books“Compelling and impressive.” —THES (Book of the Week)“An instant classic on Dutch book history.” —BMGN - Low Countries Historical Review
The Boss of Bosses: The Life of the Infamous Toto Riina Dreaded Head of the Sicilian Mafia
by Giuseppe D'Avanzo Attilio BolzoniThis is the true story of Totò Riina, the Cosa Nostra boss who rose from nothing to become the most powerful man in Sicily. The picture emerges of a bloodthirsty, power-hungry monster who, despite his lowly beginnings, is able to outmanoeuvre the other Mafia chiefs and take control of the organisation. However, the story is not just that of Riina, but also of Sicily itself. D'Avanzo and Bolzoni have transformed a complex series of events spanning several decades into a gripping narrative.In prison for 18 years now, Totò Riina still remains the dictator of the Cosa Nostra. This book tells the haunting and disturbing tale, with thorough investigation and testimony of the Sicilian Corleone.
The Bottom-up Revolution: Mastering the Emerging World of Connectivity
by Rob KallBarack Obama, Bernie Sanders, Hillary Clinton, George W. Bush, Sir Richard Branson, Steve Jobs, and Mark Zuckerberg have all said that that change or growth happen from the bottom up.But what does it mean and how do you do “bottom up” better and smarter? Bottom up is a way of life and a way of doing business. Bottom-Up: The Connection Revolution, picks up where Malcolm Gladwell’s Tipping Point left off. It is a how-to book for businesses, leaders, organizations, activists, and individuals, cracking wide-open humankind’s biggest trend in seven million years. By understanding the roots and implications of “bottom up” and “top down” you’ll be better able to tap the incredible power of this trend, as the billionaire founders of Google, Facebook, Craigslist and Twitter have done.
The Bounty Effect: 7 Steps To The Culture Of Collaboration
by Evan RosenThe Bounty Effect: 7 Steps to The Culture of Collaboration® is a much-anticipated sequel to Evan Rosen's The Culture of Collaboration®, Gold Medal Winner in the Axiom Business Book Awards. The Bounty Effect happens when exigent circumstances compel businesses, governments and organizations to change from command-and-control to collaborative. Triggers include disruptive market forces, new competitors, regional slowdowns, natural disasters, terrorist attacks and global downturns. Seize the opportunity The Bounty Effect provides. Learn how to change any organization so that every worker is a knowledge worker and each team member produces results collaboratively. See why organizations have been traveling down a well-worn road, because the new highway has yet to be built until now.
The Boy Detective: A New York Childhood
by Roger RosenblattThe Washington Post hailed Roger Rosenblatt's Making Toast as "a textbook on what constitutes perfect writing," and People lauded Kayak Morning as "intimate, expansive and profoundly moving." Classic tales of love and grief, the New York Times bestselling memoirs are also original literary works that carve out new territory at the intersection of poetry and prose. Now comes The Boy Detective, a story of the author's childhood in New York City, suffused with the same mixture of acute observation and bracing humor, lyricism and wit.Resisting the deadening silence of his family home in the elegant yet stiflingly safe neighborhood of Gramercy Park, nine-year-old Roger imagines himself a private eye in pursuit of criminals. With the dreamlike mystery of the city before him, he sets off alone, out into the streets of Manhattan, thrilling to a life of unsolved cases.Six decades later, Rosenblatt finds himself again patrolling the territory of his youth: The writing class he teaches has just wrapped up, releasing him into the winter night and the very neighborhood in which he grew up. A grown man now, he investigates his own life and the life of the city as he walks, exploring the New York of the 1950s; the lives of the writers who walked these streets before him, such as Poe and Melville; the great detectives of fiction and the essence of detective work; and the monuments of his childhood, such as the New York Public Library, once the site of an immense reservoir that nourished the city with water before it nourished it with books, and the Empire State Building, which, in Rosenblatt's imagination, vibrates sympathetically with the oversize loneliness of King Kong: "If you must fall, fall from me."As he walks, he is returned to himself, the boy detective on the case. Just as Rosenblatt invented a world for himself as a child, he creates one on this night--the writer a detective still, the chief suspect in the case of his own life, a case that discloses the shared mysteries of all our lives. A masterly evocation of the city and a meditation on memory as an act of faith, The Boy Detective treads the line between a novel and a poem, displaying a world at once dangerous and beautiful.